The CryptoMix ransomware is still alive and kicking as a new variant has been spotted being spread in the wild. This new version appends the .DLL extension to encrypted files and is said to be installed through hacked remote desktop services.
This variant was first reported in a topic in our forums where a victim stated that they were infected by the attackers hacking into their publicly exposed remote desktop services. According to the victim, the ransomware had also enabled the default administrator account and changed its password.
As ransomware continues to move away from malspam distribution and towards manual installation by hacked services or more targeted approaches, it is important to close off all publicly accessible services that can be used to gain access to Windows.
Unfortunately the CryptoMix Ransomware is still not decryptable for free. For those who wish to discuss this ransomware and receive support, you can use our dedicated Cryptomix Help & Support Topic.
The DLL Cryptomix Ransomware Variant
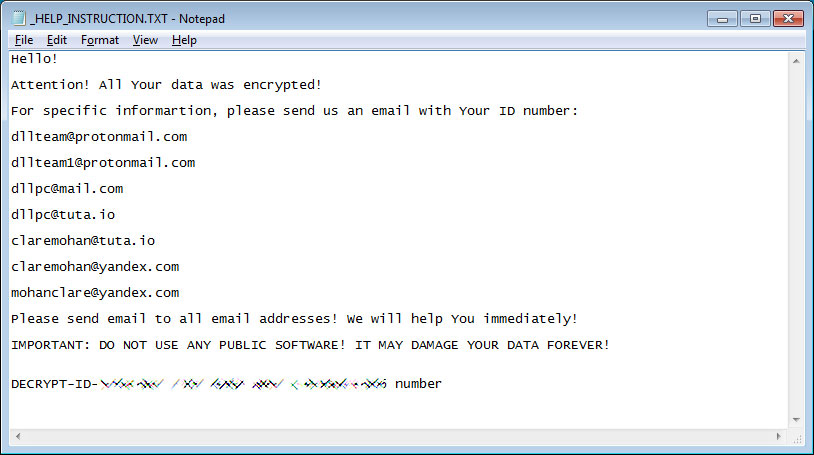
In this variant, the ransom note continues to be named _HELP_INSTRUCTIONS_.TXT, but now uses the dllteam@protonmail.com, dllteam1@protonmail.com, dllpc@mail.com, dllpc@tuta.io, laremohan@tuta.io, claremohan@yandex.com, and mohanclare@yandex.com email addresses for a victim to contact for payment information.
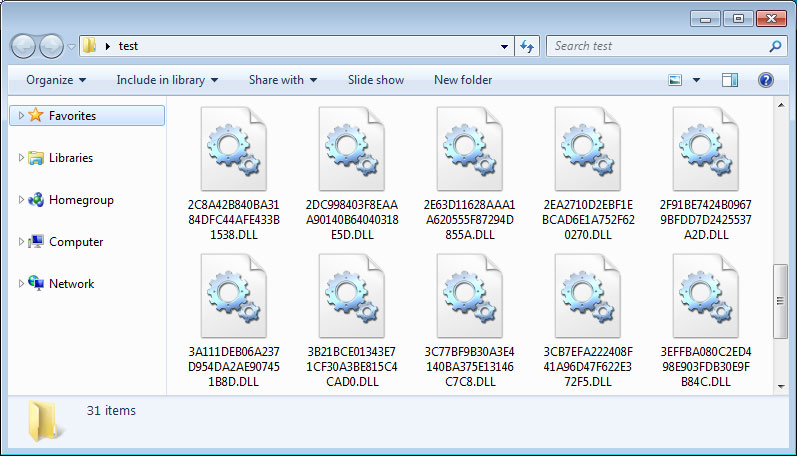
With this version, when a file is encrypted by the ransomware it will modify the filename and then append the .DLL extension to encrypted file’s name. For example, a test file encrypted by this variant has an encrypted file name of 2DC998403F8EAAA90140B64040318E5D.DLL.
Unfortunately, at this time the ransomware cannot be decrypted for free. As this is just a cursory analysis of this new variant, if anything else is discovered, we will be sure to update this article.
How to protect yourself from Ransomware
In order to protect yourself from ransomware it is important that you use good computing habits and security software. The most important step is to always have a reliable and tested backup of your data that can be restored in the case of an emergency, such as a ransomware attack.
A good security software solution that incorporates behavioral detections to combat ransomware and not just use signature detections or heuristics is important as well. For example, Emsisoft Anti-Malware and Malwarebytes Anti-Malware both contain behavioral detection that can prevent many, if not most, ransomware infections from encrypting a computer.
Last, but not least, make sure you practice the following security habits, which in many cases are the most important steps of all:
- Backup, Backup, Backup!
- Do not open attachments if you do not know who sent them.
- Do not open attachments until you confirm that the person actually sent you them,
- Scan attachments with tools like VirusTotal.
- Do not connect Remote Desktop Services directly to the Internet. Instead, make sure they can only be accessed by logging into a VPN first.
- Make sure all Windows updates are installed as soon as they come out! Also make sure you update all programs, especially Java, Flash, and Adobe Reader. Older programs contain security vulnerabilities that are commonly exploited by malware distributors. Therefore it is important to keep them updated.
- Make sure you use have some sort of security software installed that uses behavioral detections or white list technology. White listing can be a pain to train, but if your willing to stock with it, could have the biggest payoffs.
- Use hard passwords and never reuse the same password at multiple sites.
- BACKUP!
 Firewall Security Company India Complete Firewall Security Solutions Provider Company in India
Firewall Security Company India Complete Firewall Security Solutions Provider Company in India











