Android Developer Verification Rollout Begins Ahead of September Enforcement
https://firewalls.firm.in/wp-content/uploads/2026/03/android-dev.jpg

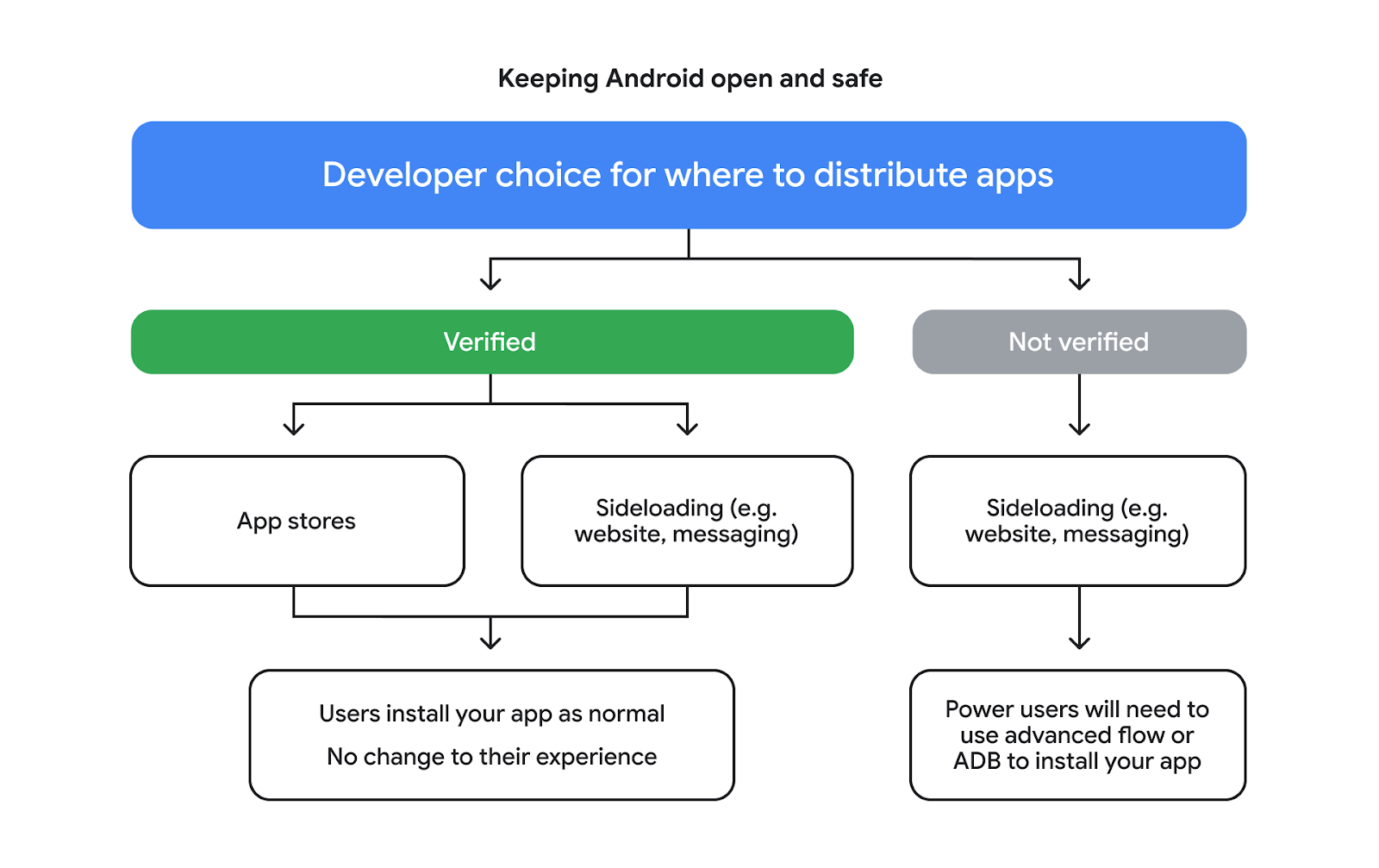
Google on Monday said it’s officially rolling out Android developer verification to all developers to combat the problem of bad actors distributing harmful apps while “hiding behind anonymity.”
The development comes ahead of a planned verification mandate that goes into effect in Brazil, Indonesia, Singapore, and Thailand this September, before it expands globally next year.
As part of this effort, Google is requiring app developers who distribute apps outside of Google Play to create an account in the Android Developer Console to confirm their identity. Those who distribute apps through Android’s official app marketplace and have verified their identity may be “already set,” the tech giant said.
“For the vast majority of users, the experience of installing apps will stay exactly the same,” Matthew Forsythe, director of product management for Android App Safety, said. “It’s only when a user tries to install an unregistered app that they’ll require ADB or advanced flow, helping us keep the broader community safe while preserving the flexibility for our power users.”
Android Studio developers can expect to see their app’s registration status right from within the integrated development environment (IDE) in the next two months when they generate a signed App Bundle or APK.
Developers who have completed Play Console’s developer verification requirements will have their eligible Play apps automatically registered. If an app cannot be registered, developers are requested to follow a manual app claim process.
As announced a couple of weeks ago, power users always have an option to enable sideloading of unregistered APK files through an advanced flow that requires an authentication step to confirm they are taking this step of their own volition and a one-off, 24-hour waiting period to deter scammers.
“This flow is a one-time process for power users – but it was designed carefully to prevent those in the midst of a scam attempt from being coerced by high-pressure tactics to install malicious software,” Forsythe said.
The development comes as Apple has revised its Developer Program License Agreement to enforce privacy rules regarding third-party wearables’ access to live activities and notifications.
Apple explicitly noted that third parties “may not use Forwarding Information for advertising, profiling, training models, or monitoring location,” adding they “may not disseminate the Forwarding Information to any other Application, or any other device besides Your Authorized Target Accessory.”
The newly added section also emphasized that developers cannot remotely store any forwarding information on a cloud service, make modifications that “materially” change the meaning of the content, or decrypt the data anywhere other than the accessory itself.
 Firewall Security Company India Complete Firewall Security Solutions Provider Company in India
Firewall Security Company India Complete Firewall Security Solutions Provider Company in India











