Vercel data breach: How hackers targeted the cloud company and offered its data for sale for $2 million https://etimg.etb2bimg.com/thumb/msid-130431427,imgsize-5766,width-1200,height=627,overlay-etciso,resizemode-75/data-breaches/vercel-data-breach-how-hackers-targeted-the-cloud-company-and-offered-its-data-for-sale-for-2-million.jpg American cloud development platform Vercel on Sunday confirmed a security breach allowing an attacker to gain unauthorised access to data for a “limited subset of customers”. “We’ve identified a security incident that involved unauthorized access to certain internal Vercel systems. We ...
Read More »Vulnerabilities & Exploits
Cybercrime Groups Using Vishing and SSO Abuse in Rapid SaaS Extortion Attacks
Cybercrime Groups Using Vishing and SSO Abuse in Rapid SaaS Extortion Attacks https://firewalls.firm.in/wp-content/uploads/2026/05/vishing.jpg Ravie LakshmananMay 01, 2026Malware / Social Engineering Cybersecurity researchers are warning of two cybercrime groups that are carrying out “rapid, high-impact attacks” operating almost within the confines of SaaS environments, while leaving minimal traces of their actions. The clusters, Cordial Spider (aka BlackFile, CL-CRI-1116, O-UNC-045, and UNC6671) ...
Read More »US security company ADT confirms hacking incident, says some customer data stolen
US security company ADT confirms hacking incident, says some customer data stolen https://etimg.etb2bimg.com/thumb/msid-130543679,imgsize-86843,width-1200,height=627,overlay-etciso,resizemode-75/data-breaches/us-security-company-adt-confirms-hacking-incident-says-some-customer-data-stolen.jpg ADT, one of the largest home security providers in the US, has confirmed that hackers successfully broke into its systems and stole customer information like their phone numbers and addresses. The announcement comes as a notorious extortion group, known as ShinyHunters, threatens to leak millions of records ...
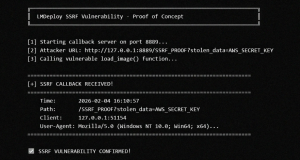
Read More »LMDeploy CVE-2026-33626 Flaw Exploited Within 13 Hours of Disclosure
LMDeploy CVE-2026-33626 Flaw Exploited Within 13 Hours of Disclosure https://firewalls.firm.in/wp-content/uploads/2026/04/lmdeploy.png A high-severity security flaw in LMDeploy, an open-source toolkit for compressing, deploying, and serving LLMs, has come under active exploitation in the wild less than 13 hours after its public disclosure. The vulnerability, tracked as CVE-2026-33626 (CVSS score: 7.5), relates to a Server-Side Request Forgery (SSRF) vulnerability that could be ...
Read More »China supercomputer breach exposes massive defence data, sparks security concerns
China supercomputer breach exposes massive defence data, sparks security concerns https://etimg.etb2bimg.com/thumb/msid-130168248,imgsize-172930,width-1200,height=627,overlay-etciso,resizemode-75/data-breaches/china-supercomputer-breach-exposes-massive-defence-data-sparks-security-concerns.jpg A major cybersecurity breach has reportedly exposed highly sensitive data from a Chinese government supercomputer, raising serious concerns around national security and data protection. The story reported by CNN broke out recently. According to reports, a hacker managed to infiltrate a system linked to the National Supercomputing Centre in ...
Read More »$13.74M Hack Shuts Down Sanctioned Grinex Exchange After Intelligence Claims
$13.74M Hack Shuts Down Sanctioned Grinex Exchange After Intelligence Claims https://firewalls.firm.in/wp-content/uploads/2026/04/grinex.jpg Ravie LakshmananApr 18, 2026Money Laundering / Regulatory Compliance Grinex, a Kyrgyzstan-incorporated cryptocurrency exchange sanctioned by the U.K. and the U.S. last year, said it’s suspending operations after it blamed Western intelligence agencies for a $13.74 million hack. The exchange said it fell victim to what it described as a ...
Read More »FBI shuts down ready-made kit that imitated login pages and stole millions from users worldwide
FBI shuts down ready-made kit that imitated login pages and stole millions from users worldwide https://etimg.etb2bimg.com/thumb/msid-130226818,imgsize-8416,width-1200,height=627,overlay-etciso,resizemode-75/data-breaches/fbi-shuts-down-ready-made-kit-that-imitated-login-pages-and-stole-millions-from-users-worldwide.jpg The FBI Atlanta Field Office, working closely with Indonesian law enforcement, has dismantled a highly organized global phishing operation that gave cybercriminals easy access to a powerful tool for stealing account credentials and attempting large-scale fraud. At the centre of the operation was a ...
Read More »[Webinar] Eliminate Ghost Identities Before They Expose Your Enterprise Data
[Webinar] Eliminate Ghost Identities Before They Expose Your Enterprise Data https://firewalls.firm.in/wp-content/uploads/2026/04/ghost.jpg Mohit KumarApr 18, 2026Artificial Intelligence / Enterprise Security In 2024, compromised service accounts and forgotten API keys were behind 68% of cloud breaches. Not phishing. Not weak passwords. Unmanaged non-human identities that nobody was watching. For every employee in your org, there are 40 to 50 automated credentials: service accounts, API tokens, ...
Read More »Meta pauses all work with AI recruiting startup Mercor after $10 billion company confirms hacking
Meta pauses all work with AI recruiting startup Mercor after $10 billion company confirms hacking https://etimg.etb2bimg.com/thumb/msid-130050239,imgsize-7718,width-1200,height=627,overlay-etciso,resizemode-75/data-breaches/meta-pauses-all-work-with-ai-recruiting-startup-mercor-after-10-billion-company-confirms-hacking.jpg Meta has indefinitely suspended all work with Mercor. This comes after the artificial intelligence (AI) data contracting startup valued at $10 billion confirmed a security breach that may have exposed proprietary training data belonging to some of the world’s most prominent AI laboratories. According ...
Read More »Multi-OS Cyberattacks: How SOCs Close a Critical Risk in 3 Steps
Multi-OS Cyberattacks: How SOCs Close a Critical Risk in 3 Steps https://firewalls.firm.in/wp-content/uploads/2026/04/cyberattacks.jpg Your attack surface no longer lives on one operating system, and neither do the campaigns targeting it. In enterprise environments, attackers move across Windows endpoints, executive MacBooks, Linux infrastructure, and mobile devices, taking advantage of the fact that many SOC workflows are still fragmented by platform. For security leaders, this creates a costly operational gap: ...
Read More » Firewall Security Company India Complete Firewall Security Solutions Provider Company in India
Firewall Security Company India Complete Firewall Security Solutions Provider Company in India