Millions of infected devices fueled massive cyberattacks https://etimg.etb2bimg.com/thumb/msid-129691490,imgsize-11922,width-1200,height=627,overlay-etciso,resizemode-75/data-breaches/us-says-it-disrupted-botnets-that-infected-over-3-million-devices-worldwide.jpg The U.S. Justice Department on Thursday said it took part in an operation with Germany and Canada to take down infrastructure used by four major botnets that infected more than 3 million devices worldwide, including hundreds of thousands in the U.S. The malicious networks – Aisuru, KimWolf, JackSkid and Mossad – were ...
Read More »Vulnerabilities & Exploits
Hackers Exploit CVE-2025-32975 (CVSS 10.0) to Hijack Unpatched Quest KACE SMA Systems
Hackers Exploit CVE-2025-32975 (CVSS 10.0) to Hijack Unpatched Quest KACE SMA Systems https://firewalls.firm.in/wp-content/uploads/2026/03/kace.jpg Ravie LakshmananMar 23, 2026Vulnerability / Endpoint Security Threat actors are suspected to be exploiting a maximum-severity security flaw impacting Quest KACE Systems Management Appliance (SMA), according to Arctic Wolf. The cybersecurity company said it observed malicious activity starting the week of March 9, 2026, in customer environments ...
Read More »TRU identifies mobile spyware campaign using fake Red Alert app in Israel
TRU identifies mobile spyware campaign using fake Red Alert app in Israel https://etimg.etb2bimg.com/thumb/msid-129603786,imgsize-5482,width-1200,height=627,overlay-etciso,resizemode-75/data-breaches/tru-identifies-mobile-spyware-campaign-using-fake-red-alert-app-in-israel.jpg A targeted smishing campaign has been identified in which Israeli users received SMS messages impersonating official Home Front Command alerts and distributing a trojanized version of Israel’s Red Alert rocket warning Android app. The malicious app preserves the legitimate rocket alert functionality, making it harder for users ...
Read More »AI Flaws in Amazon Bedrock, LangSmith, and SGLang Enable Data Exfiltration and RCE
AI Flaws in Amazon Bedrock, LangSmith, and SGLang Enable Data Exfiltration and RCE https://firewalls.firm.in/wp-content/uploads/2026/03/lang-ai.jpg Cybersecurity researchers have disclosed details of a new method for exfiltrating sensitive data from artificial intelligence (AI) code execution environments using domain name system (DNS) queries. In a report published Monday, BeyondTrust revealed that Amazon Bedrock AgentCore Code Interpreter’s sandbox mode permits outbound DNS queries that ...
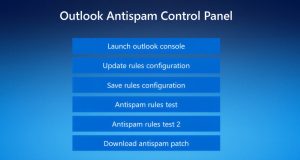
Read More »Fake Tech Support Spam Deploys Customized Havoc C2 Across Organizations
Fake Tech Support Spam Deploys Customized Havoc C2 Across Organizations https://firewalls.firm.in/wp-content/uploads/2026/03/outlook.jpg Threat hunters have called attention to a new campaign as part of which bad actors masqueraded as fake IT support to deliver the Havoc command-and-control (C2) framework as a precursor to data exfiltration or ransomware attack. The intrusions, identified by Huntress last month across five partner organizations, involved the ...
Read More »Building a High-Impact Tier 1: The 3 Steps CISOs Must Follow
Building a High-Impact Tier 1: The 3 Steps CISOs Must Follow https://firewalls.firm.in/wp-content/uploads/2026/03/tier1.jpg Every CISO knows the uncomfortable truth about their Security Operations Center: the people most responsible for catching threats in real time are the people with the least experience. Tier 1 analysts sit at the front line of detection, and yet they are also the most vulnerable to the ...
Read More »Microsoft Warns OAuth Redirect Abuse Delivers Malware to Government Targets
Microsoft Warns OAuth Redirect Abuse Delivers Malware to Government Targets https://firewalls.firm.in/wp-content/uploads/2026/03/ms-login.jpg Ravie LakshmananMar 03, 2026Phishing / Malware Microsoft on Monday warned of phishing campaigns that employ phishing emails and OAuth URL redirection mechanisms to bypass conventional phishing defenses implemented in email and browsers. The activity, the company said, targets government and public-sector organizations with the end goal of redirecting victims ...
Read More »⚡ Weekly Recap: SD-WAN 0-Day, Critical CVEs, Telegram Probe, Smart TV Proxy SDK and More
⚡ Weekly Recap: SD-WAN 0-Day, Critical CVEs, Telegram Probe, Smart TV Proxy SDK and More https://firewalls.firm.in/wp-content/uploads/2026/03/recap-main.jpg Ravie LakshmananMar 02, 2026Cybersecurity / Hacking This week is not about one big event. It shows where things are moving. Network systems, cloud setups, AI tools, and common apps are all being pushed in different ways. Small gaps in access control, exposed keys, and ...
Read More »How to Protect Your SaaS from Bot Attacks with SafeLine WAF
How to Protect Your SaaS from Bot Attacks with SafeLine WAF https://firewalls.firm.in/wp-content/uploads/2026/03/safeline.jpg Most SaaS teams remember the day their user traffic started growing fast. Few notice the day bots started targeting them. On paper, everything looks great: more sign-ups, more sessions, more API calls. But in reality, something feels off: Sign-ups increase, but users aren’t activating. Server costs rise faster ...
Read More »Thousands of Public Google Cloud API Keys Exposed with Gemini Access After API Enablement
Thousands of Public Google Cloud API Keys Exposed with Gemini Access After API Enablement https://firewalls.firm.in/wp-content/uploads/2026/03/gemini.jpg New research has found that Google Cloud API keys, typically designated as project identifiers for billing purposes, could be abused to authenticate to sensitive Gemini endpoints and access private data. The findings come from Truffle Security, which discovered nearly 3,000 Google API keys (identified by ...
Read More » Firewall Security Company India Complete Firewall Security Solutions Provider Company in India
Firewall Security Company India Complete Firewall Security Solutions Provider Company in India