Enterprises move from securing data to proving trust: Leaders unpack the new competitive advantage at ETCISO DP&P Summit 2025 https://etimg.etb2bimg.com/thumb/msid-125930618,imgsize-88480,width-1200,height=627,overlay-etciso,resizemode-75/data-breaches/enterprises-move-from-securing-data-to-proving-trust-leaders-unpack-the-new-competitive-advantage-at-etciso-dpp-summit-2025.jpg At the ET CISO Data Protection & Privacy Summit 2025, senior leaders from fintech, insurance, banking, market infrastructure and digital identity platforms examined how trust is shifting from a moral position to a measurable business strategy. Moderated by Sneha Jha, ...
Read More »Vulnerabilities & Exploits
Phantom Stealer Spread by ISO Phishing Emails Hitting Russian Finance Sector
Phantom Stealer Spread by ISO Phishing Emails Hitting Russian Finance Sector https://firewalls.firm.in/wp-content/uploads/2025/12/email.jpg Dec 15, 2025Ravie LakshmananMalware / Cybercrime Cybersecurity researchers have disclosed details of an active phishing campaign that’s targeting a wide range of sectors in Russia with phishing emails that deliver Phantom Stealer via malicious ISO optical disc images. The activity, codenamed Operation MoneyMount-ISO by Seqrite Labs, has primarily ...
Read More »Personal data is not property—but CISOs must treat it with utmost responsibility’: Justice B. N. Srikrishna at ET CISO Data Protection & Privacy Summit 2025
Personal data is not property—but CISOs must treat it with utmost responsibility’: Justice B. N. Srikrishna at ET CISO Data Protection & Privacy Summit 2025 https://etimg.etb2bimg.com/thumb/msid-125927799,imgsize-54080,width-1200,height=627,overlay-etciso,resizemode-75/data-breaches/justice-b-n-srikrishna-personal-data-responsibility-and-the-role-of-cisos-at-et-ciso-data-protection-privacy-summit-2025.jpg At the ET CISO Data Protection & Privacy Summit 2025, Hon’ble Justice (Retd.) B. N. Srikrishna—the architect of India’s foundational data protection framework—delivered a sweeping keynote on the evolving philosophy of personal data and ...
Read More »Android Malware FvncBot, SeedSnatcher, and ClayRat Gain Stronger Data Theft Features
Android Malware FvncBot, SeedSnatcher, and ClayRat Gain Stronger Data Theft Features https://firewalls.firm.in/wp-content/uploads/2025/12/android-malware.jpg Cybersecurity researchers have disclosed details of two new Android malware families dubbed FvncBot and SeedSnatcher, as another upgraded version of ClayRat has been spotted in the wild. The findings come from Intel 471, CYFIRMA, and Zimperium, respectively. FvncBot, which masquerades as a security app developed by mBank, targets ...
Read More »Digital battlefield: Data dominance, codebreaking and the roots of information warfare
Digital battlefield: Data dominance, codebreaking and the roots of information warfare https://etimg.etb2bimg.com/thumb/msid-125684785,imgsize-255746,width-1200,height=627,overlay-etciso,resizemode-75/data-breaches/digital-battlefield-data-dominance-codebreaking-and-the-roots-of-information-warfare.jpg Negligence in data handling leads to large scale data exposure, enabling malicious actors to exploit leaked data for committing fraud, blackmail or identity theft triggering penal statutes. Data is often described as the ‘new oil’ – a strategic asset central to the survival of individuals, corporations or even ...
Read More »ThreatsDay Bulletin: AI Malware, Voice Bot Flaws, Crypto Laundering, IoT Attacks — and 20 More Stories
ThreatsDay Bulletin: AI Malware, Voice Bot Flaws, Crypto Laundering, IoT Attacks — and 20 More Stories https://firewalls.firm.in/wp-content/uploads/2025/11/threatsday.jpg Nov 27, 2025Ravie LakshmananCybersecurity / Hacking News Hackers have been busy again this week. From fake voice calls and AI-powered malware to huge money-laundering busts and new scams, there’s a lot happening in the cyber world. Criminals are getting creative — using smart ...
Read More »Comcast to pay $1.5 million US fine after vendor data breach
Comcast to pay $1.5 million US fine after vendor data breach https://etimg.etb2bimg.com/thumb/msid-125554889,imgsize-65124,width-1200,height=627,overlay-etciso,resizemode-75/data-breaches/comcast-to-pay-1-5-million-us-fine-after-vendor-data-breach.jpg Comcast will pay a $1.5 million fine after a vendor breach exposed personal data from 237,000 current and former customers, the Federal Communications Commission said on Monday. The FCC said a debt collector used by Comcast until 2022, Financial Business and Consumer Solutions, suffered a 2024 data breach ...
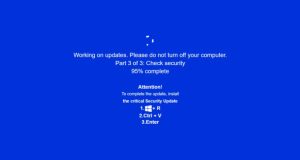
Read More »JackFix Uses Fake Windows Update Pop-Ups on Adult Sites to Deliver Multiple Stealers
JackFix Uses Fake Windows Update Pop-Ups on Adult Sites to Deliver Multiple Stealers https://firewalls.firm.in/wp-content/uploads/2025/11/update-windows.jpg Cybersecurity researchers are calling attention to a new campaign that’s leveraging a combination of ClickFix lures and fake adult websites to deceive users into running malicious commands under the guise of a “critical” Windows security update. “Campaign leverages fake adult websites (xHamster, PornHub clones) as its ...
Read More »Clearview AI faces criminal complaint in Austria for suspected privacy violations
Clearview AI faces criminal complaint in Austria for suspected privacy violations https://etimg.etb2bimg.com/thumb/msid-124886388,imgsize-24704,width-1200,height=627,overlay-etciso,resizemode-75/data-breaches/clearview-ai-faces-criminal-complaint-in-austria-for-suspected-privacy-violations.jpg An Austrian privacy group has filed a criminal complaint against Clearview AI. Austrian privacy group noyb said on Tuesday it has filed a criminal complaint in Austria, accusing US-based Clearview AI of illegally collecting photos and videos of European Union residents to build its facial-recognition database. Noyb said ...
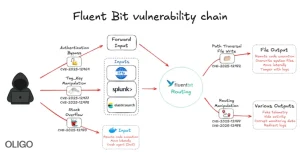
Read More »New Fluent Bit Flaws Expose Cloud to RCE and Stealthy Infrastructure Intrusions
New Fluent Bit Flaws Expose Cloud to RCE and Stealthy Infrastructure Intrusions https://firewalls.firm.in/wp-content/uploads/2025/11/bit-main.jpg Nov 24, 2025Ravie LakshmananVulnerability / Container Security Cybersecurity researchers have discovered five vulnerabilities in Fluent Bit, an open-source and lightweight telemetry agent, that could be chained to compromise and take over cloud infrastructures. The security defects “allow attackers to bypass authentication, perform path traversal, achieve remote code ...
Read More » Firewall Security Company India Complete Firewall Security Solutions Provider Company in India
Firewall Security Company India Complete Firewall Security Solutions Provider Company in India