WatchGuard Firewall Support Services Provider in India WatchGuard Firewall Support WatchGuard is an advanced technology-based firewall that offers an exceptional level of security to your system. In the event, if a WatchGuard firewall user faces any issue, they can share their queries at WatchGuard firewall support services. Here, are the professionals round the clock available for the customers to troubleshoot ...
Read More »Cyber Security
SonicWall Firewall Support India
SonicWall Firewall Support Services Provider in India SonicWall Firewall Support SonicWall Firewall Support Are you using Sonicwall firewall and facing some issues regarding it? If yes, then you have reached the right place. We are one of the prominent SonicWall firewall support service providers, who always readily available to resolve the technical issues that you are facing right now. The ...
Read More »Fortinet Firewall Support
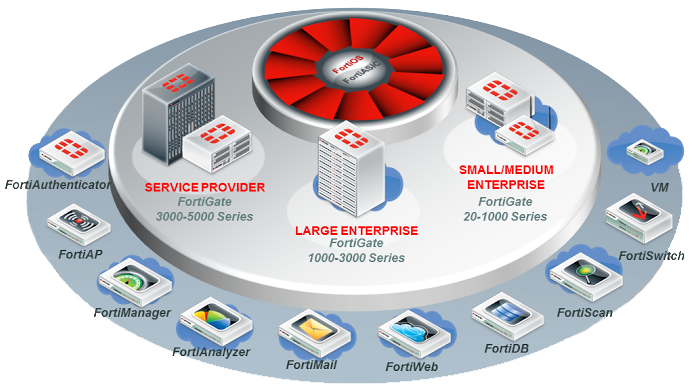
Fortinet Firewall Support Fortinet Firewall Support Services Provider in India Fortinet Firewall support services: It’s amazing to know that how firewalls protects our system from the external threats and keep our data safe. There are so many firewalls in the market, but when it comes to advanced technology based firewalls, FortiGate is the best. In the event, if you ...
Read More »Hire a Firewall Engineer
Hire a Firewall Engineer An up-to-date firewall can help you protect your organization’s network while allowing legitimate business communication to be sent and received. It keeps bad actors out and can be used to keep employees away from insecure or non-work-related sites. While a firewall provides excellent security and protection, it needs monitoring and management. Monitoring your own firewall ...
Read More »Firewall Consultant
Firewall Consultants in India An up-to-date firewall can help you protect your organization’s network while allowing legitimate business communication to be sent and received. It keeps bad actors out and can be used to keep employees away from insecure or non-work-related sites. While a firewall provides excellent security and protection, it needs monitoring and management. Monitoring your own firewall ...
Read More »Firewall Support India
Firewall Support India Firewall support number : +91 94 8585 7788, +91 94 8585 7788 Firewall Support Service in India Managed Firewall Support Services : – This emergency support service allows your business to function securely without interruption. Our service covers everything from troubleshooting to firewall administration. Firewall Firm Managed Firewall Services offer a suite of cost effective methods to ...
Read More »VAPT Services Provider Company in India
VAPT Services Provider Company in India VULNERABILITY ASSESSMENT is a process to evaluate the security risks in the software system in order to reduce the probability of a threat. It is also called Vulnerability Testing. A vulnerability is any mistakes or weakness in the system security procedures, design, implementation or any internal control that may result in the violation of ...
Read More »VAPT Companies in India
VAPT Companies in India Firewall Firm, a Best VAPT Companies in India, Providing VAPT Services in India. VULNERABILITY ASSESSMENT is a process to evaluate the security risks in the software system in order to reduce the probability of a threat. It is also called Vulnerability Testing. A vulnerability is any mistakes or weakness in the system security procedures, design, implementation ...
Read More »Top 10 SIEM Tools
Top 10 SIEM (Security Information and Event Management) Tools The more insight you have into your business operations, the safer you are. Security Information and Event Management Systems are crucial solutions for the digital world. They’re designed to tie your systems together and provide a more comprehensive view of IT security. By 2021, the SIEM market will be worth $5.93 ...
Read More »Firewall Support
Hardware & Software Firewall installation, configuration and Remote Support Services Customer satisfaction is Firewall Firm’s s number one priority. Firewall Firm’s Support Services provide global support for all Configuring Software and Hardware Firewall products and its support services. Firewalls also Prevent Computer Viruses on Internet gateway level with benefits of Advanced Anti Malware and phishing attacks, Learn about firewalls, malware, ...
Read More » Firewall Security Company India Complete Firewall Security Solutions Provider Company in India
Firewall Security Company India Complete Firewall Security Solutions Provider Company in India