Safeguarding Your Organization from Shadow AI Risks, ETCISO
Your biggest AI threat in 2026 isn’t an external attacker. It’s your own employees.
Let me start with the problem nobody wants to talk about in board meetings.
BlackFog’s January 2026 research found that 86% of employees now use AI tools weekly for work. 49% admit to using tools their employer hasn’t approved. And 58% of those use free versions that offer no enterprise data protection. Microsoft’s research shows 75% of workers already use AI at work, with 78% bringing their own tools.
Those numbers are alarming enough. But here’s where it gets genuinely dangerous.
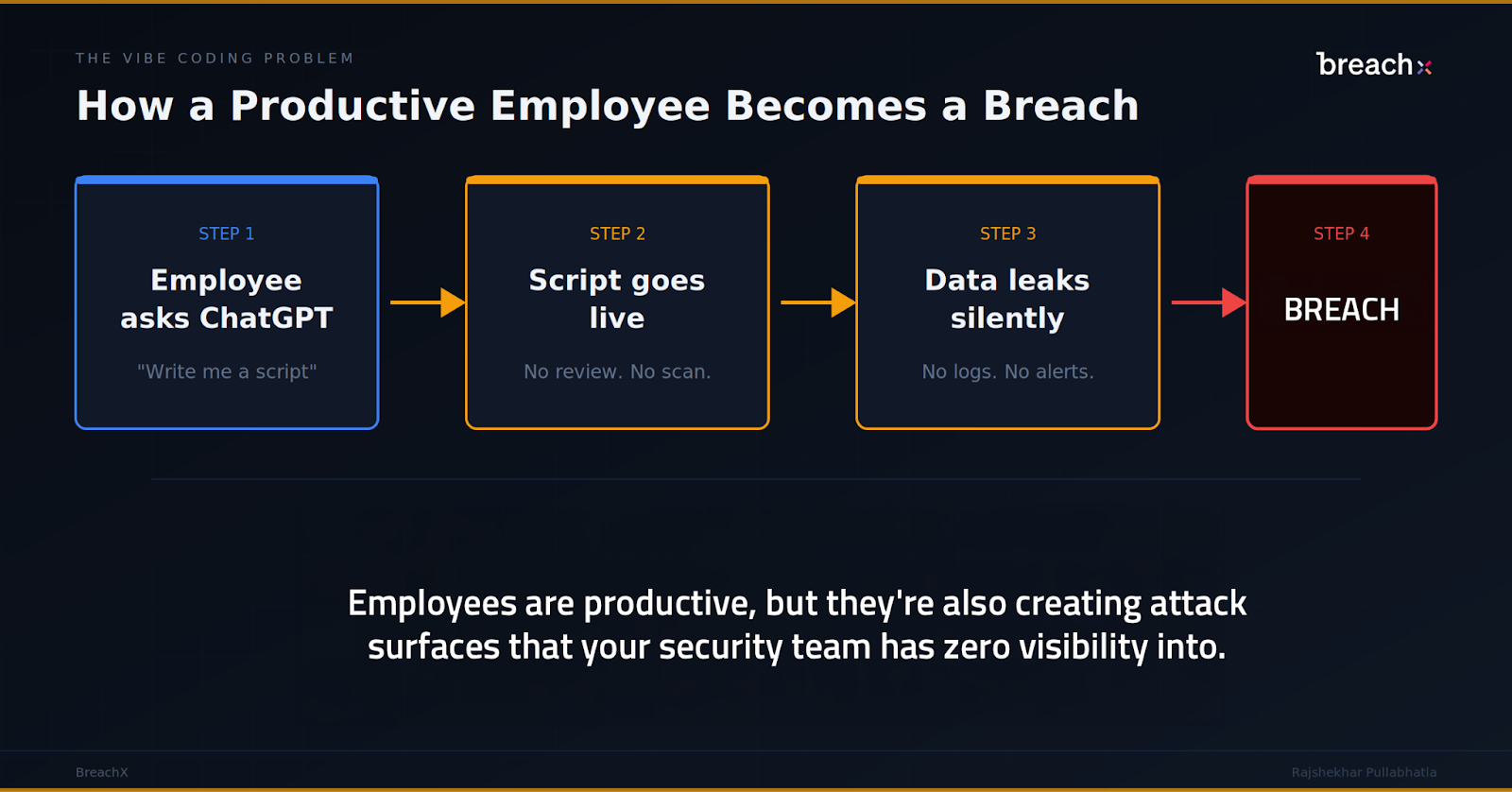
Non-technical employees are now “vibe coding.” A marketing analyst uses ChatGPT to write a Python script that scrapes prospect data and pipes it into the CRM. A finance team member builds a quick automation that pulls confidential datasets into an AI tool for analysis. A developer pastes proprietary source code into a free AI assistant for debugging (Samsung learned this the hard way when employees uploaded proprietary code to ChatGPT). None of these people are malicious. They’re productive. They’re also creating attack surfaces that your security team has zero visibility into.
IBM’s global study quantified the damage: shadow AI added $670,000 to the average breach cost in organisations where it was present. 20% of organisations reported breaches specifically caused by shadow AI. Only 37% have any governance or detection policies in place.
Cisco’s State of AI Security report found that over 25% of the 30,000+ AI agent “skills” they analysed contained at least one vulnerability. These are the plug-ins and extensions that AI tools use to interact with enterprise systems. One compromised skill can give an attacker a direct path into your infrastructure through a tool your own employee installed.
The prediction: by late 2026, “shadow AI breach” will become a recognised incident category in its own right, distinct from insider threat or data leakage. The first high-profile Indian enterprise breach attributed to vibe-coded, unvetted internal tooling will happen within the next 12 months. The CISO won’t have known the tool existed.
What to do: banning AI is not the answer. BlackFog found that 63% of employees believe it’s acceptable to use AI without IT oversight if no approved alternative exists. The answer is to provide enterprise-grade alternatives that are genuinely comparable to the consumer tools, establish clear data classification for AI interactions, and deploy real-time monitoring. When one healthcare system provided approved AI tools, unauthorised use dropped 89%
The sovereign AI divide is about to reshape your vendor shortlist.
Every major cybersecurity vendor is scrambling to answer a question that didn’t exist two years ago: where does the AI in your security product train, run, and store data?
CrowdStrike announced sovereign cloud deployments for India, Saudi Arabia, and the UAE at Davos in January 2026, with pilot customers in government and finance rolling out through 2026. Saudi Arabia’s $40 billion AI investment fund and the UAE’s Stargate project with OpenAI are building national AI infrastructure at unprecedented scale. India’s IndiaAI Mission is pushing for sovereign AI capabilities across finance, defence, and healthcare.
McKinsey estimates that 30-40% of all AI spending, roughly $500-600 billion globally by 2030, will be influenced by sovereignty requirements. IDC forecasts that by 2028, 60% of organisations with data sovereignty mandates will have migrated sensitive workloads to new environments.
For Indian CISOs, this creates a practical problem right now. Your current security stack likely sends telemetry, threat data, and potentially sensitive logs to servers outside India. Under the Digital Personal Data Protection Act, this is increasingly untenable for sensitive workloads. But switching to sovereign alternatives means evaluating whether localised AI models can match the detection quality of globally trained ones.
The prediction: by end of 2026, at least two major global cybersecurity vendors will lose significant Indian enterprise contracts specifically because they cannot demonstrate in-country data residency for their AI-powered features. CISOs who start evaluating sovereign-capable alternatives now will avoid painful mid-contract migrations later.
The Iran-Israel-US conflict is not a Middle Eastern problem. It’s your problem.
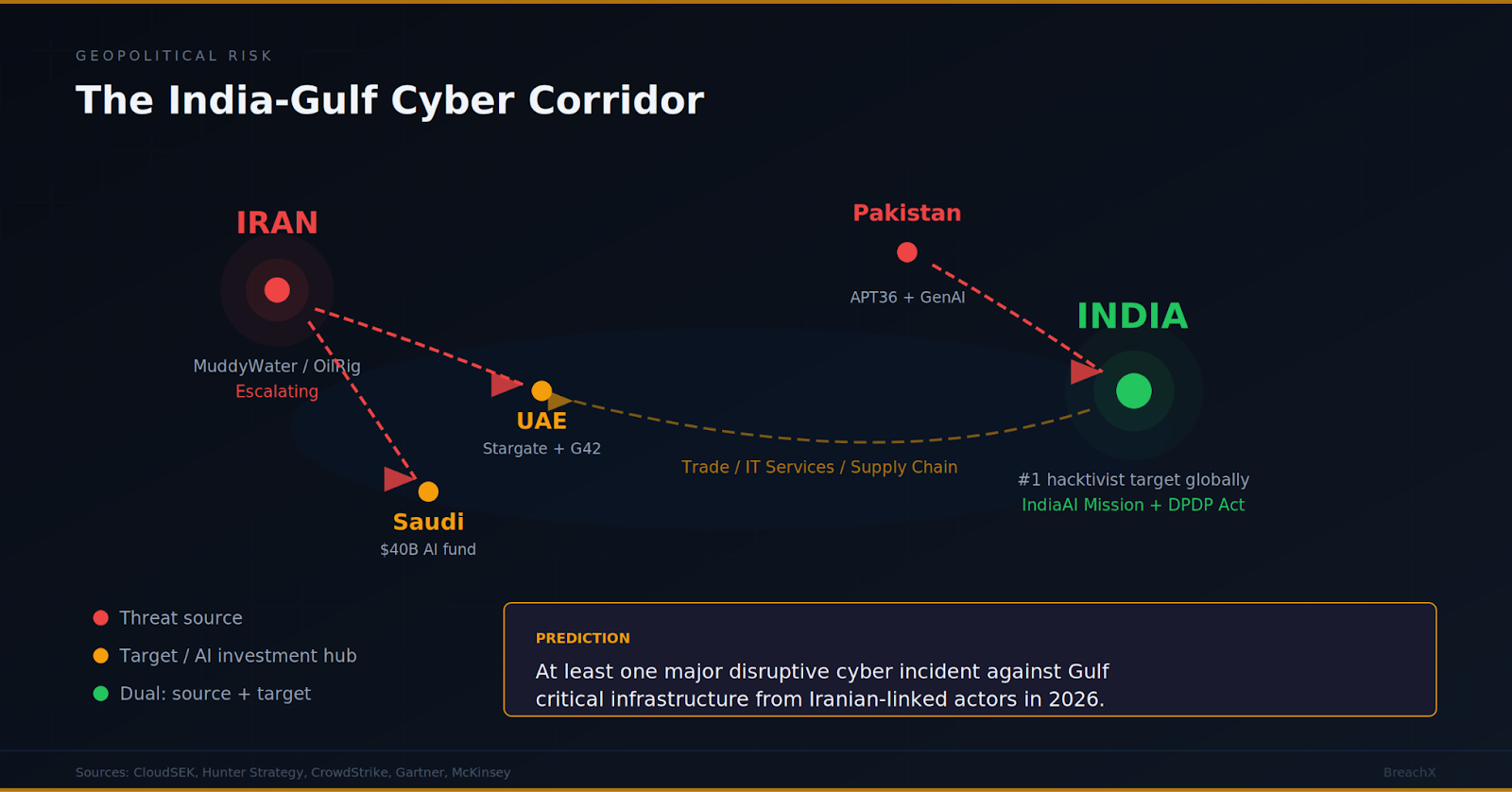
If your enterprise operates in or with partners across the Gulf, the cyber dimension of the Iran-Israel-US conflict directly affects you.
Following Operation Lion’s Roar, Iranian APT groups have escalated cyber operations against Gulf critical infrastructure. MuddyWater, OilRig, APT33, and APT42 are all targeting energy, telecom, maritime, and financial sectors across the UAE, Saudi Arabia, and Qatar. CloudSEK and Hunter Strategy have both documented this surge in early 2026.
Apply the geopolitical escalation ladder here: when kinetic conflict intensifies, cyber operations follow a predictable sequence. Hacktivism first, then targeted espionage, then pre-positioning inside OT and critical infrastructure, then potential disruption. Iran has moved to stage three. Cyber Av3ngers and Fox Kitten have already demonstrated capability against water utilities and VPN infrastructure.
For Indian enterprises, the Gulf is not a distant market. It’s where billions in trade, services, and IT infrastructure contracts flow. DP World, Etihad, ADNOC, Saudi Aramco’s supply chains all include Indian IT service providers. A successful Iranian cyber operation against Gulf port infrastructure doesn’t just affect Dubai. It affects every Indian company with shipments, contracts, or employees in the region.
The prediction: at least one majr disruptive cyber incident against Gulf critical infrastructure (energy, ports, or telecom) attributable to Iranian-linked actors will occur in 2026. Indian enterprises with Gulf exposure need to model this into their business continuity plans now, not after it happens.
What to kill, what to keep, and where to invest.
Here’s where I’ll be direct about product and investment decisions. These are my views based on the data, not vendor recommendations.
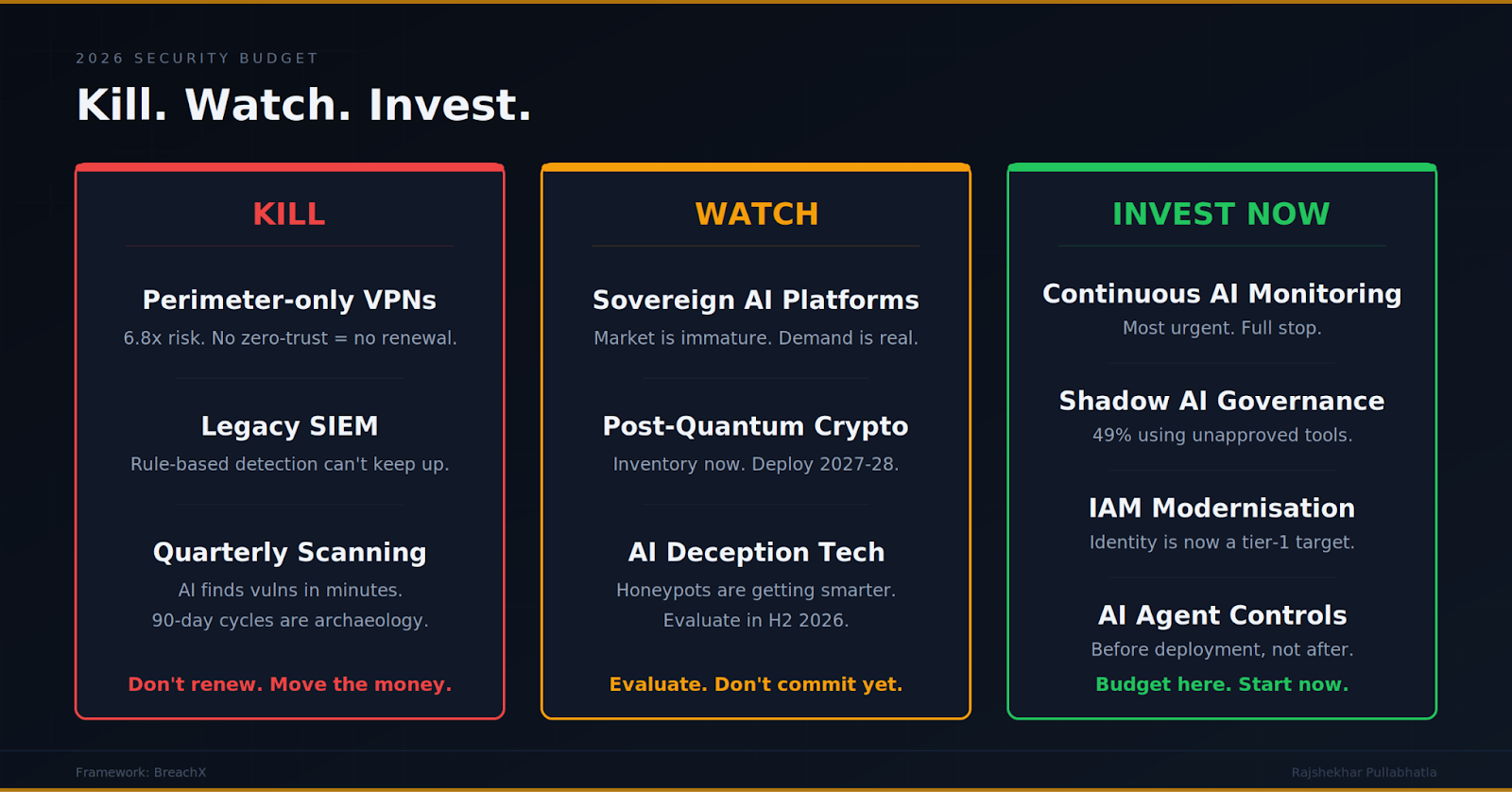
Kill or let expire in 2026:
Traditional perimeter-only VPN solutions without zero-trust integration. The 6.8x risk multiplier for on-prem VPN users (Eclypsium) and CISA’s BOD 26-02 ordering removal of end-of-support edge devices are not subtle signals. If your VPN renewal is coming up and it doesn’t include ZTNA capabilities, don’t renew. Redirect that budget.
Legacy SIEM platforms that rely on rule-based detection without AI/ML-powered anomaly detection. The speed of AI-equipped attackers means signature-based detection is now a trailing indicator, not a defence. If your SIEM can’t detect behavioural anomalies in real time, it’s generating expensive false comfort.
Point-solution vulnerability scanners running on quarterly schedules. When AI finds vulnerabilities in minutes and exploits ship on the day of disclosure, a quarterly scan is an archaeological exercise. You’re documenting what already happened, not preventing what’s coming.
Invest in now:
Continuous AI-powered vulnerability monitoring and attack surface management. This is the most time-critical investment. The gap between AI-powered offence and periodic human-driven assessment is widening every month.
Shadow AI detection and governance tooling. With 86% of employees using AI weekly and 49% using unapproved tools (BlackFog), this is not optional. You need visibility into what AI tools are running in your environment, what data they’re touching, and whether they meet your security and compliance standards.
Identity and access management modernisation. When attackers compromise the identity platform, they don’t need another exploit. BeyondTrust, VMware Aria Operations, and Microsoft identity products were all added to the CISA KEV catalog in early 2026. Your IAM infrastructure is now a tier-1 attack target.
AI-specific security controls for agentic deployments. Cisco found that 83% of organisations plan to deploy agentic AI but only 29% are ready to secure it. If your organisation is deploying AI agents that access enterprise systems, you need controls around agent permissions, data boundaries, and behaviour monitoring before deployment, not after.
Watch and evaluate for late 2026:
Sovereign AI security platforms from Indian and regional vendors. The market is immature but the demand is clear. CrowdStrike, Palo Alto, and others are racing to establish local cloud presence in India. Local startups building AI-powered security with in-country data residency will emerge as serious alternatives. Evaluate them, but don’t bet your stack on them yet.
Post-quantum cryptography readiness. Not urgent for 2026, but Palo Alto Networks flags it as a planning priority. Start inventory of cryptographic assets and dependencies so you’re not starting from zero when quantum-capable adversaries arrive.
The Real Conclusion
The cybersecurity industry loves to talk about AI as both sword and shield. The uncomfortable truth is simpler than that.
AI has made the cost of attacking you dramatically cheaper, the speed of attacks dramatically faster, the number of people who can attack you dramatically larger, and the number of ways your own employees can accidentally expose you dramatically higher. All at once. All in 2026.
Your response to this can’t be a bigger budget spent on the same categories. It has to be a different budget spent on different things. Kill what’s obsolete. Invest where the threat has moved. And accept that the most dangerous AI in your organisation might be the one your marketing team subscribed to last Tuesday.
The author is Rajshekhar Pullabhatla, Founder of BreachX.
Disclaimer: The views expressed are solely of the author and ETCISO does not necessarily subscribe to it. ETCISO shall not be responsible for any damage caused to any person/organization directly or indirectly.
 Firewall Security Company India Complete Firewall Security Solutions Provider Company in India
Firewall Security Company India Complete Firewall Security Solutions Provider Company in India












