What is Firewall?
What is Firewall?
What is Firewall?
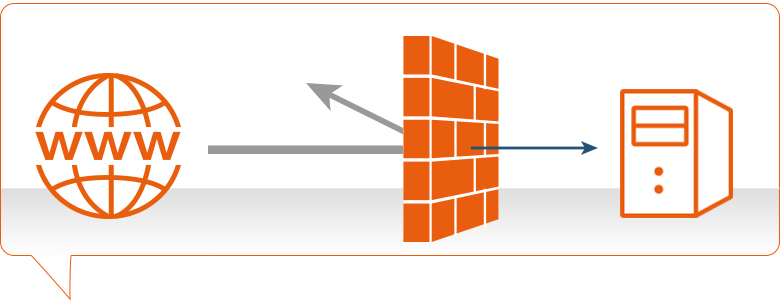
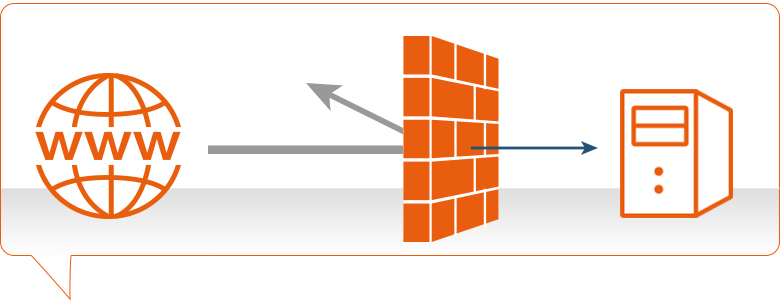
Firewall, What is Firewall? A firewall is a network security device located between your internal network and the wider Internet. A firewall monitors incoming and outgoing network traffic – blocking or allowing it based on a set of configurable rules.
Firewalls are a fundamental piece of security and typically form the first line of defense on a network. Acting as a filter against bad connections from the outside world.
A firewall works by comparing the data sent into or out of the network against a list of rules. Based on the results of the rule checking, the firewall will then either block or allow the connection.
How Does Firewall Work?
Introduction – What is Firewall?
A firewall is a system that provides network security by filtering incoming and outgoing network traffic based on a set of user-defined rules. In general, the purpose of a firewall is to reduce or eliminate the occurrence of unwanted network communications while allowing all legitimate communication to flow freely. In most server infrastructures, firewalls provide an essential layer of security that, combined with other measures, prevent attackers from accessing your servers in malicious ways.
This guide will discuss how firewalls work, with a focus on stateful software firewalls, such as iptables and FirewallD, as they relate to cloud servers. We’ll start with a brief explanation of TCP packets and the different types of firewalls. Then we’ll discuss a variety of topics that a relevant to stateful firewalls. Lastly, we will provide links to other tutorials that will help you set up a firewall on your own server.
TCP Network Packets
Before discussing the different types of firewalls, let’s take a quick look at what Transport Control Protocol (TCP) network traffic looks like.
TCP network traffic moves around a network in packets, which are containers that consist of a packet header—this contains control information such as source and destination addresses, and packet sequence information—and the data (also known as a payload). While the control information in each packet helps to ensure that its associated data gets delivered properly, the elements it contains also provides firewalls a variety of ways to match packets against firewall rules.
It is important to note that successfully receiving incoming TCP packets requires the receiver to send outgoing acknowledgment packets back to the sender. The combination of the control information in the incoming and outgoing packets can be used to determine the connection state (e.g. new, established, related) of between the sender and receiver.
What is firewall? Types of Firewalls
Let’s quickly discuss the three basic types of network firewalls: packet filtering (stateless), stateful, and application layer.
Packet filtering, or stateless, firewalls work by inspecting individual packets in isolation. As such, they are unaware of connection state and can only allow or deny packets based on individual packet headers.
Stateful firewalls are able to determine the connection state of packets, which makes them much more flexible than stateless firewalls. They work by collecting related packets until the connection state can be determined before any firewall rules are applied to the traffic.
Application firewalls go one step further by analyzing the data being transmitted, which allows network traffic to be matched against firewall rules that are specific to individual services or applications. These are also known as proxy-based firewalls.
In addition to firewall software, which is available on all modern operating systems, firewall functionality can also be provided by hardware devices, such as routers or firewall appliances. Again, our discussion will be focused on stateful software firewalls that run on the servers that they are intended to protect.
Firewall Rules
As mentioned above, network traffic that traverses a firewall is matched against rules to determine if it should be allowed through or not. An easy way to explain what firewall rules looks like is to show a few examples, so we’ll do that now.
Suppose you have a server with this list of firewall rules that apply to incoming traffic:
- Accept new and established incoming traffic to the public network interface on port 80 and 443 (HTTP and HTTPS web traffic)
- Drop incoming traffic from IP addresses of the non-technical employees in your office to port 22 (SSH)
- Accept new and established incoming traffic from your office IP range to the private network interface on port 22 (SSH)
Note that the first word in each of these examples is either “accept”, “reject”, or “drop”. This specifies the action that the firewall should do in the event that a piece of network traffic matches a rule. Accept means to allow the traffic through, reject means to block the traffic but reply with an “unreachable” error, and drop means to block the traffic and send no reply. The rest of each rule consists of the condition that each packet is matched against.
As it turns out, network traffic is matched against a list of firewall rules in a sequence, or chain, from first to last. More specifically, once a rule is matched, the associated action is applied to the network traffic in question. In our example, if an accounting employee attempted to establish an SSH connection to the server they would be rejected based on rule 2, before rule 3 is even checked. A system administrator, however, would be accepted because they would match only rule 3.
Default Policy
It is typical for a chain of firewall rules to not explicitly cover every possible condition. For this reason, firewall chains must always have a default policy specified, which consists only of an action (accept, reject, or drop).
Suppose the default policy for the example chain above was set to drop. If any computer outside of your office attempted to establish an SSH connection to the server, the traffic would be dropped because it does not match the conditions of any rules.
If the default policy were set to accept, anyone, except your own non-technical employees, would be able to establish a connection to any open service on your server. This would be an example of a very poorly configured firewall because it only keeps a subset of your employees out.
Incoming and Outgoing Traffic
As network traffic, from the perspective of a server, can be either incoming or outgoing, a firewall maintains a distinct set of rules for either case. Traffic that originates elsewhere, incoming traffic, is treated differently than outgoing traffic that the server sends. It is typical for a server to allow most outgoing traffic because the server is usually, to itself, trustworthy. Still, the outgoing rule set can be used to prevent unwanted communication in the case that a server is compromised by an attacker or a malicious executable.
In order to maximize the security benefits of a firewall, you should identify all of the ways you want other systems to interact with your server, create rules that explicitly allow them, then drop all other traffic. Keep in mind that the appropriate outgoing rules must be in place so that a server will allow itself to send outgoing acknowledgements to any appropriate incoming connections. Also, as a server typically needs to initiate its own outgoing traffic for various reasons—for example, downloading updates or connecting to a database—it is important to include those cases in your outgoing rule set as well.
Writing Outgoing Rules
Suppose our example firewall is set to drop outgoing traffic by default. This means our incoming accept rules would be useless without complementary outgoing rules.
To complement the example incoming firewall rules (1 and 3), from the Firewall Rules section, and allow proper communication on those addresses and ports to occur, we could use these outgoing firewall rules:
- Accept established outgoing traffic to the public network interface on port 80 and 443 (HTTP and HTTPS)
- Accept established outgoing traffic to the private network interface on port 22 (SSH)
Note that we don’t need to explicitly write a rule for incoming traffic that is dropped (incoming rule 2) because the server doesn’t need to establish or acknowledge that connection.
What is firewall? Firewall Software and Tools
Now that we’ve gone over how firewalls work, let’s take a look at common software packages that can help us set up an effective firewall. While there are many other firewall-related packages, these are effective and are the ones you will encounter the most.
Iptables
Iptables is a standard firewall included in most Linux distributions by default (a modern variant called nftables will begin to replace it). It is actually a front end to the kernel-level netfilter hooks that can manipulate the Linux network stack. It works by matching each packet that crosses the networking interface against a set of rules to decide what to do.
To learn how to implement a firewall with iptables, check out these links:
- How To Set Up a Firewall Using IPTables on Ubuntu 14.04
- How To Implement a Basic Firewall Template with Iptables on Ubuntu 14.04
- How To Set Up an Iptables Firewall to Protect Traffic Between your Servers
UFW
UFW, which stands for Uncomplicated Firewall, is an interface to iptables that is geared towards simplifying the process of configuring a firewall.
To learn more about using UFW, check out this tutorial: How To Setup a Firewall with UFW on an Ubuntu and Debian Cloud Server.
FirewallD
FirewallD is a complete firewall solution available by default on CentOS 7 servers. Incidentally, FirewallD uses iptables to configure netfilter.
To learn more about using FirewallD, check out this tutorial: How To Configure FirewallD to Protect Your CentOS 7 Server.
If you’re running CentOS 7 but prefer to use iptables, follow this tutorial: How To Migrate from FirewallD to Iptables on CentOS 7.
Fail2ban
Fail2ban is an intrusion prevention software that can automatically configure your firewall to block brute force login attempts and DDOS attacks.
To learn more about Fail2ban, check out these links:
- How Fail2ban Works to Protect Services on a Linux Server
- How To Protect SSH with Fail2Ban on Ubuntu 14.04
- How To Protect an Nginx Server with Fail2Ban on Ubuntu 14.04
- How To Protect an Apache Server with Fail2Ban on Ubuntu 14.04
Conclusion
Now that you understand how firewalls work, you should look into implementing a firewall that will improve your security of your server setup by using the tutorials above.
A firewall is a software program or piece of hardware that helps screen out hackers, viruses, and worms that try to reach your computer over the Internet. If you can’t start Windows Firewall or you are getting an error, use Microsoft free tool to diagnose and fix problems.
- If you use a computer at home, the most effective and important first step you can take to help protect your computer is to turn on a firewall.
- Windows 8, Windows 7, Windows Vista, and Windows XP SP2 or higher have a firewall built-in and turned on by default. (Note: Support for Windows XP ended in April 2014.)
- If you have more than one computer connected in the home, or if you have a small-office network, it is important to protect every computer. You should have a hardware firewall (such as a router) to protect your network, but you should also use a software firewall on each computer to help prevent the spread of a virus in your network if one of the computers becomes infected.
- If your computer is part of a business, school, or other organizational network, you should follow the policy established by the network administrator.
Automatically diagnose and fix problems with Windows Firewall
-
- Select the Download button on this page.
- In the File Download dialog box, click Run or Open, and then follow the steps in the Windows Firewall Troubleshooter.
- This troubleshooter might be in English only. However, the automatic fix also works for versions of Windows in other languages.
- If you’re not on the computer that has the problem, save the troubleshooter to a flash drive or a CD, and then run it on the computer that has the problem.
-
- Windows Firewall isn’t the default firewall
- Windows Firewall doesn’t start
- Windows couldn’t start Windows Firewall (Service-specific error 5 (0x5))
- Remote Assistance isn’t working because it’s blocked by Windows Firewall
- You’re unable to access shared files and printers because sharing is blocked by Windows Firewall
- BFE service is missing
- Firewall won’t start (Error Code 80070424)
-
- Windows 7
- Windows 8
- Windows 8.1
- Windows 10
What is firewall?
A firewall is a network security device located between your internal network and the wider Internet. A firewall monitors incoming and outgoing network traffic – blocking or allowing it based on a set of configurable rules.
Firewalls are a fundamental piece of security and typically form the first line of defence on a network. Acting as a filter against bad connections from the outside world.
A firewall works by comparing the data sent into or out of the network against a list of rules. Based on the results of the rule checking, the firewall will then either block or allow the connection.
What is firewall? How does a firewall work?
Firewalls work by inspecting data packets (small chunks of data) against an internal list of rules. Here are some of the more common ones:
- IP addresses – filter out traffic from suspicious IPs
- Domain names – block traffic from known malicious domains
- Ports – deny traffic trying to enter through a certain port
- Contents – block data packets containing certain keywords
A firewall scans the contents of the packet and then determines whether to let it through based on the rules in place. On a typical network setup, all connections to the Internet flow through the firewall. Meaning it inspects all inbound or outgoing packets.
How does firewall inspection work?
The process of inspection involves comparing a packet’s contents against the firewall’s set of rules. Depending on if the rule is setup as a blacklist or whitelist, it will react differently to a match.
- A blacklist rule will block any packets which match the criteria.
- A whitelist rule will block any packets which don’t match the criteria.
A firewall’s rules are highly configurable. Meaning you can make the packet inspection process unique to your security setup. Here are some examples of how you could use custom firewall rules:
- Creating a whitelist for your own company IP. Preventing any outsiders from accessing what’s behind the firewall.
- Making a blacklist for the IP of a known malicious file server. Stopping it from distributing malware onto your network.
- Creating a whitelist for certain domain extensions (.com, .co.uk .edu e.t.c.) on outgoing traffic. Blocking staff from accessing potentially dangerous sites.
Why are firewalls important?
Firewalls are often compared to a lock on the door to your network. But it might be more accurate to say that a firewall is the door.
Without a firewall in place, any connection can flow freely in or out of your network. Including connections from known malicious sources. This means you could experience unauthorised access to networked files. Leading to a data breach, malware infection or worse.
You need a firewall to filter out the bulk of malicious connections. And there’s a lot of malicious connections. One study found that within 52 seconds of being online, servers were being probed by hackers. With an average rate of 757 connection attempts per hour.
Are firewalls hardware or software?
Firewalls can be either a hardware appliance or a piece of software which runs on a machine. So, the answer is both.
Not helpful, I know.
But the main difference between the two is this:
- Software firewalls tend to protect the individual machine it’s installed upon, typically a laptop or PC
- Hardware firewalls usually protect many machines or an entire network.
What types of firewall are there?
Circuit-level
Circuit level firewalls are a type of firewall that monitors transmission control protocol (TCP) handshaking. It ensures that the communication between packets is legitimate and not malicious.
Stateful inspection
A firewall with stateful inspection considers the state of current connections when filtering packets. This means that the firewall can block the packet in one case but allowed in another. Depending on the current state of the connection.
Unified threat management (UTM)
Whilst technically not a type of firewall, UTM is instead an advanced security appliance which combines the security functions of many different security appliances. One of these being a firewall. We have an article explaining everything you need to know about UTM if you wish to learn more.
What is a next-generation firewall?
A next-generation firewall (NGFW) contains all the normal defences that a traditional firewall has and more. The most common additions are intrusion prevention software and application control. But certain vendors have other bonus security features. NGFWs are also capable of deep packet inspection which enables more robust filters.
Intrusion prevention software monitors network activity to detect and stop vulnerability exploits from occurring. This is usually done by monitoring for breaches against the network policies in place.
Application control software sets up a hard filter for programs that can send or receive data over the Internet. This can either be done by blacklist (blocks any programs in the filter) or by whitelist (blocks any programs not in the filter).
What is deep packet inspection?
Deep Packet Inspection (DPI) is a type of packet inspection which analyses the full contents of a data packet. Instead of only information in a packet’s header (where it is coming from and going to).
This enables DPI to filter out malicious packets, such as viruses and trojans, with better accuracy. As rather than only looking at the sender and destination, the packet’s contents can be used in filters as well.
This allows DPI to uncover a broader range of security threats because it will discover packets with a malicious payload but an innocuous header.
Where did the name firewall come from?
A final piece of trivia: the name firewall originated from the real-world application of fire partitions used in buildings. These would be walls that were implemented into a building to act as a barrier to stop fire spreading from one room to another.
The similarity between a fire spreading through a building and a computer virus spreading through a network prompted the same name to be adopted for the network device.
Firewall
Firewall
What is Firewall?
A firewall is a network security device located between your internal network and the wider Internet. A firewall monitors incoming and outgoing network traffic – blocking or allowing it based on a set of configurable rules.
Firewalls are a fundamental piece of security and typically form the first line of defence on a network. Acting as a filter against bad connections from the outside world.
A firewall works by comparing the data sent into or out of the network against a list of rules. Based on the results of the rule checking, the firewall will then either block or allow the connection.
How does a firewall work?
Firewalls work by inspecting data packets (small chunks of data) against an internal list of rules. Here are some of the more common ones:
- IP addresses – filter out traffic from suspicious IPs
- Domain names – block traffic from known malicious domains
- Ports – deny traffic trying to enter through a certain port
- Contents – block data packets containing certain keywords
A firewall scans the contents of the packet and then determines whether to let it through based on the rules in place. On a typical network setup, all connections to the Internet flow through the firewall. Meaning it inspects all inbound or outgoing packets.
How does firewall inspection work?
The process of inspection involves comparing a packet’s contents against the firewall’s set of rules. Depending on if the rule is setup as a blacklist or whitelist, it will react differently to a match.
- A blacklist rule will block any packets which match the criteria.
- A whitelist rule will block any packets which don’t match the criteria.
A firewall’s rules are highly configurable. Meaning you can make the packet inspection process unique to your security setup. Here are some examples of how you could use custom firewall rules:
- Creating a whitelist for your own company IP. Preventing any outsiders from accessing what’s behind the firewall.
- Making a blacklist for the IP of a known malicious file server. Stopping it from distributing malware onto your network.
- Creating a whitelist for certain domain extensions (.com, .co.uk .edu e.t.c.) on outgoing traffic. Blocking staff from accessing potentially dangerous sites.
Why are firewalls important?
Firewalls are often compared to a lock on the door to your network. But it might be more accurate to say that a firewall is the door.
Without a firewall in place, any connection can flow freely in or out of your network. Including connections from known malicious sources. This means you could experience unauthorised access to networked files. Leading to a data breach, malware infection or worse.
You need a firewall to filter out the bulk of malicious connections. And there’s a lot of malicious connections. One study found that within 52 seconds of being online, servers were being probed by hackers. With an average rate of 757 connection attempts per hour.
Are firewalls hardware or software?
Firewalls can be either a hardware appliance or a piece of software which runs on a machine. So, the answer is both.
Not helpful, I know.
But the main difference between the two is this:
- Software firewalls tend to protect the individual machine it’s installed upon, typically a laptop or PC
- Hardware firewalls usually protect many machines or an entire network.
What types of firewall are there?
Circuit-level
Circuit level firewalls are a type of firewall that monitors transmission control protocol (TCP) handshaking. It ensures that the communication between packets is legitimate and not malicious.
Stateful inspection
A firewall with stateful inspection considers the state of current connections when filtering packets. This means that the firewall can block the packet in one case but allowed in another. Depending on the current state of the connection.
Unified threat management (UTM)
Whilst technically not a type of firewall, UTM is instead an advanced security appliance which combines the security functions of many different security appliances. One of these being a firewall. We have an article explaining everything you need to know about UTM if you wish to learn more.
What is a next-generation firewall?
A next-generation firewall (NGFW) contains all the normal defences that a traditional firewall has and more. The most common additions are intrusion prevention software and application control. But certain vendors have other bonus security features. NGFWs are also capable of deep packet inspection which enables more robust filters.
Intrusion prevention software monitors network activity to detect and stop vulnerability exploits from occurring. This is usually done by monitoring for breaches against the network policies in place.
Application control software sets up a hard filter for programs that can send or receive data over the Internet. This can either be done by blacklist (blocks any programs in the filter) or by whitelist (blocks any programs not in the filter).
What is deep packet inspection?
Deep Packet Inspection (DPI) is a type of packet inspection which analyses the full contents of a data packet. Instead of only information in a packet’s header (where it is coming from and going to).
This enables DPI to filter out malicious packets, such as viruses and trojans, with better accuracy. As rather than only looking at the sender and destination, the packet’s contents can be used in filters as well.
This allows DPI to uncover a broader range of security threats because it will discover packets with a malicious payload but an innocuous header.
Where did the name firewall come from?
A final piece of trivia: the name firewall originated from the real-world application of fire partitions used in buildings. These would be walls that were implemented into a building to act as a barrier to stop fire spreading from one room to another.
The similarity between a fire spreading through a building and a computer virus spreading through a network prompted the same name to be adopted for the network device.
 Firewall Security Company India Complete Firewall Security Solutions Provider Company in India
Firewall Security Company India Complete Firewall Security Solutions Provider Company in India
















