
A firewall should be part of your overall cyber security mitigation strategy. You’re not a big bank or Apple, so your business is safe from hackers. Right? Unfortunately not. Many hackers actually target smaller to medium organizations because they know SMEs are less likely to invest in cyber security.
So how can you protect your business and client information from falling into the wrong hands? A firewall can help form part of your overall strategy.
What is a firewall?
A firewall is a network security system that controls incoming and outgoing traffic on a computer or business network. This control is based on a set of policies or rules. These policies or rules are configured on the firewall or via the firewall management console.
A firewall basically helps protect the devices, applications and data that sit behind it on the internal network. This can be at your office or between offices or even services you have sitting at your hosting provider or cloud provider.
Installing a firewall on your network or in front of your cloud services means you are helping protect your users and data on the network from nasty attacks and vulnerabilities from the internet.

11 TOP Firewall Features for your Business
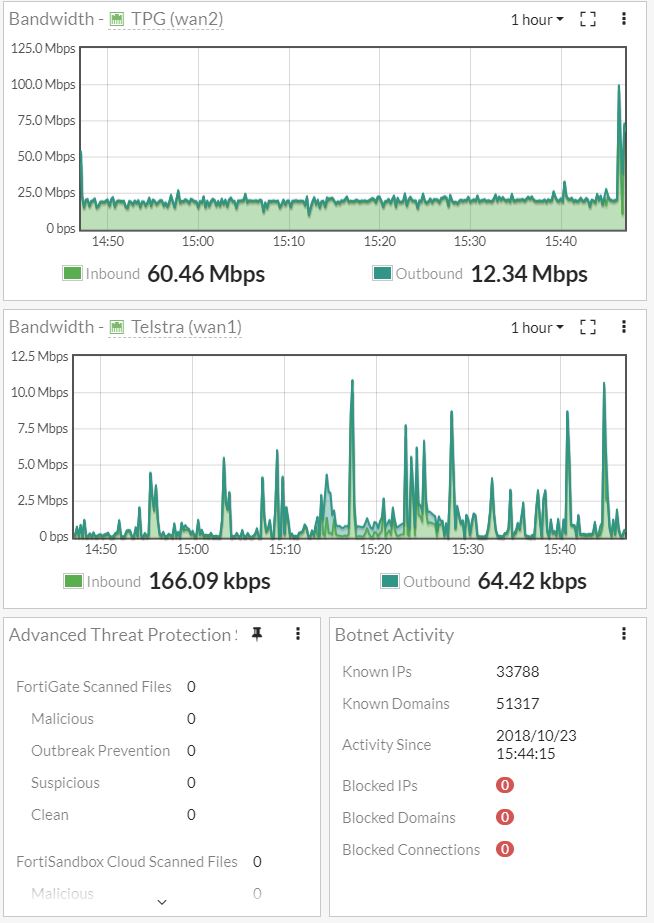
1. Bandwidth control and monitoring
Bandwidth control or sometimes it can be referred to as traffic shaping is one of the best. We don’t always have unlimited amounts of bandwidth so it’s vital to take control of the bandwidth available. With a firewall you can control bandwidth available for sites, applications and users.
You may want to give your graphics department more overall bandwidth. Or you might want to stop cloud based file synchronization services from hammering your bandwidth. Things line OneDrive, DropBox and Google Drive can cause serious issues.
With bandwidth control on your firewall you can allocate a set amount of dedicated bandwidth for your VoIP phone system. You can even allow other cloud based services like Skype for Business or Hangouts to have priority. This will help stop the dreaded jitter that makes any phone or video call painful.
You can control when backups for example happen between sites so that those backups aren’t causing problems during business hours. You can allow backups to have a large chunk of the connection out of hours.
You could enforce backup traffic to travel over cheaper links. And more important traffic can be set to go over your higher quality links when quality really matters.
2. Web filtering
Most firewalls allow you to block access to websites. This can be done on a case by case basis or your firewall can include a subscription that helps you choose categories you don’t want people to have access to. Such as illegal activities, downloading illegal content, gambling and many many more.
The firewall vendor will continuously update their lists for you as those types of websites will always be updating their IP addresses and domain names. Vendors like Cisco and Fortigate take the hassle out of this for you with their automatic updated lists.
3. Logging
Having access to logs on a firewall gives you up to the minute information about what is happening on your network. Good firewalls give graphs in real time and they also show you what vulnerabilities or attack are happening in real time.
4. Internet aggregation and SD WAN
Link aggregation and SD WAN is a great feature for businesses who need multiple links to the internet. Or where you are using multiple links and you would like to connect to other sites such as branch offices or cloud services.
The ability to use multiple links allows you to have redundancy or even use multiple cheap links with different providers to meet your bandwidth requirements.
5. Sandboxing
Sandboxing takes a file or executable as your are downloading and opens it in a completely isolated and separate environment. This environment replicates the end user environment away from your production environment without putting your users at risk. A sandbox then opens it, runs it scans it and looks for malware or activity that is suspicious.
If the files or link looks ok it will pass it on to the end user. Sandboxing is one of those things that the end users have no idea is there but it is another layer protecting them from a cyber attack.
6. Integrated wireless controller
Using a firewall with an integrated wireless controller is a fantastic way to save money and bring all of your policies and control into one place or platform.
You can easily setup different SSIDs, policies and take full control over your environment. Depending on the model of firewall you choose will depend on how many wireless access points you can use. Low entry level models will allow 2-10 access points and larger high end models will allow hundreds.
You can even setup all of your sites using the same policies so your users can roam between sites without any need to connect or enter in passwords at each site.
7. Deep Packet Inspection
Deep packet inspection is a great feature we just can’t live without anymore. This technology allows the firewall to really take a close look at the packet that is being passed though.
It can look for hidden viruses, and malicious activity that is hidden within the packet. The firewall can then decide what to do with the packet. It can block the sender or drop the packet.
The really great thing is if the firewall determines it’s a new source threat it will sent a note back to the vendor that will then be reviewed and update other firewalls around the world helping other networks keep safe.
8. Virtual Private Networks
Virtual private networks (VPN) are great for users connecting back to a site or the office. VPNs can also be used to connect two sites together.
You want to make sure that device if it’s another network/firewall or if it’s an end user computer that it is secure and safe. With a VPN you can allow users to access applications and data securely from remote locations. And best of all you aren’t opening up public facing ports or applications.
9. Malware and virus filtering
Next generation firewalls are always filtering for malware new and old. Viruses, compromised websites, files containing viruses, bot nets trying to hack you, man in the middle attacks you name it! They can even scan encrypted traffic such as SSL and TLS connections to make sure they are safe and trusted.
10. Intrusion prevention system
Intrusion prevention systems (IPS) is the latest advancements from intrusion detection systems (IDS).
Intrusion prevention goes one better by monitoring the network traffic using policies. It looks for suspicious activity. If it detects suspicious activity on a network it will block the traffic and then provide a report.
11. Identity management integration and single sign on
One of the greatest features is that firewalls allow you to integrate with single sign on platforms either directly or via a radius server. If you have an environment where cyber security is paramount and you are controlling your users by department or function or even site then integrating their access into group management and single sign on cuts down the administrative overhead.
A firewall can never guarantee the safety of your data, it does provide a greater chance of keeping it safe. If you can’t afford to lose your data, or suffer a breach of confidential data, then a firewall will help form part of your overall cyber security mitigation strategy.
 Firewall Security Company India Complete Firewall Security Solutions Provider Company in India
Firewall Security Company India Complete Firewall Security Solutions Provider Company in India











