84% of female entrepreneurs use UPI; cohort shows the highest levels of digital adoption: Report https://etimg.etb2bimg.com/thumb/msid-129193057,imgsize-1994229,width-1200,height=627,overlay-etciso,resizemode-75/data-breaches/majority-of-female-entrepreneurs-embrace-digital-banking-despite-concerns-over-data-privacy.jpg In a report by DBS Bank India, HNW (High-Net-Worth) women, female entrepreneurs, and rural women were surveyed. Among these participants, 31% of female entrepreneurs reported a monthly personal income ranging between Rs 1 lakh and Rs 3 lakh. 27% of HNW women had an ...
Read More »Vulnerabilities & Exploits
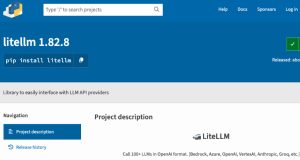
TeamPCP Backdoors LiteLLM Versions 1.82.7–1.82.8 Likely via Trivy CI/CD Compromise
TeamPCP Backdoors LiteLLM Versions 1.82.7–1.82.8 Likely via Trivy CI/CD Compromise https://firewalls.firm.in/wp-content/uploads/2026/03/lite.jpg TeamPCP, the threat actor behind the recent compromises of Trivy and KICS, has now compromised a popular Python package named litellm, pushing two malicious versions containing a credential harvester, a Kubernetes lateral movement toolkit, and a persistent backdoor. Multiple security vendors, including Endor Labs and JFrog, revealed that litellm ...
Read More »Cognizant unit TriZetto breach exposes data of 3.4m people
Cognizant unit TriZetto breach exposes data of 3.4m people https://etimg.etb2bimg.com/thumb/msid-129309061,imgsize-7510,width-1200,height=627,overlay-etciso,resizemode-75/data-breaches/cognizant-unit-trizetto-breach-exposes-data-of-3-4m-people.jpg Bengaluru: Cognizant subsidiary TriZetto Provider Solutions (TPS) has suffered a data breach that exposed the sensitive information of about 3.4 million individuals, according to a filing with the Office of the Maine Attorney General. TPS said it has begun notifying affected individuals about the cybersecurity incident, which may have exposed ...
Read More »⚡ Weekly Recap: CI/CD Backdoor, FBI Buys Location Data, WhatsApp Ditches Numbers & More
⚡ Weekly Recap: CI/CD Backdoor, FBI Buys Location Data, WhatsApp Ditches Numbers & More https://firewalls.firm.in/wp-content/uploads/2026/03/recap-bl.jpg Ravie LakshmananMar 23, 2026Cybersecurity / Hacking Another week, another reminder that the internet is still a mess. Systems people thought were secure are being broken in simple ways, showing many still ignore basic advisories. This edition covers a mix of issues: supply chain attacks hitting ...
Read More »Millions of infected devices fueled massive cyberattacks
Millions of infected devices fueled massive cyberattacks https://etimg.etb2bimg.com/thumb/msid-129691490,imgsize-11922,width-1200,height=627,overlay-etciso,resizemode-75/data-breaches/us-says-it-disrupted-botnets-that-infected-over-3-million-devices-worldwide.jpg The U.S. Justice Department on Thursday said it took part in an operation with Germany and Canada to take down infrastructure used by four major botnets that infected more than 3 million devices worldwide, including hundreds of thousands in the U.S. The malicious networks – Aisuru, KimWolf, JackSkid and Mossad – were ...
Read More »Hackers Exploit CVE-2025-32975 (CVSS 10.0) to Hijack Unpatched Quest KACE SMA Systems
Hackers Exploit CVE-2025-32975 (CVSS 10.0) to Hijack Unpatched Quest KACE SMA Systems https://firewalls.firm.in/wp-content/uploads/2026/03/kace.jpg Ravie LakshmananMar 23, 2026Vulnerability / Endpoint Security Threat actors are suspected to be exploiting a maximum-severity security flaw impacting Quest KACE Systems Management Appliance (SMA), according to Arctic Wolf. The cybersecurity company said it observed malicious activity starting the week of March 9, 2026, in customer environments ...
Read More »TRU identifies mobile spyware campaign using fake Red Alert app in Israel
TRU identifies mobile spyware campaign using fake Red Alert app in Israel https://etimg.etb2bimg.com/thumb/msid-129603786,imgsize-5482,width-1200,height=627,overlay-etciso,resizemode-75/data-breaches/tru-identifies-mobile-spyware-campaign-using-fake-red-alert-app-in-israel.jpg A targeted smishing campaign has been identified in which Israeli users received SMS messages impersonating official Home Front Command alerts and distributing a trojanized version of Israel’s Red Alert rocket warning Android app. The malicious app preserves the legitimate rocket alert functionality, making it harder for users ...
Read More »AI Flaws in Amazon Bedrock, LangSmith, and SGLang Enable Data Exfiltration and RCE
AI Flaws in Amazon Bedrock, LangSmith, and SGLang Enable Data Exfiltration and RCE https://firewalls.firm.in/wp-content/uploads/2026/03/lang-ai.jpg Cybersecurity researchers have disclosed details of a new method for exfiltrating sensitive data from artificial intelligence (AI) code execution environments using domain name system (DNS) queries. In a report published Monday, BeyondTrust revealed that Amazon Bedrock AgentCore Code Interpreter’s sandbox mode permits outbound DNS queries that ...
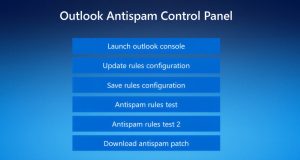
Read More »Fake Tech Support Spam Deploys Customized Havoc C2 Across Organizations
Fake Tech Support Spam Deploys Customized Havoc C2 Across Organizations https://firewalls.firm.in/wp-content/uploads/2026/03/outlook.jpg Threat hunters have called attention to a new campaign as part of which bad actors masqueraded as fake IT support to deliver the Havoc command-and-control (C2) framework as a precursor to data exfiltration or ransomware attack. The intrusions, identified by Huntress last month across five partner organizations, involved the ...
Read More »Building a High-Impact Tier 1: The 3 Steps CISOs Must Follow
Building a High-Impact Tier 1: The 3 Steps CISOs Must Follow https://firewalls.firm.in/wp-content/uploads/2026/03/tier1.jpg Every CISO knows the uncomfortable truth about their Security Operations Center: the people most responsible for catching threats in real time are the people with the least experience. Tier 1 analysts sit at the front line of detection, and yet they are also the most vulnerable to the ...
Read More » Firewall Security Company India Complete Firewall Security Solutions Provider Company in India
Firewall Security Company India Complete Firewall Security Solutions Provider Company in India