Top 10 SIEM (Security Information and Event Management) Tools
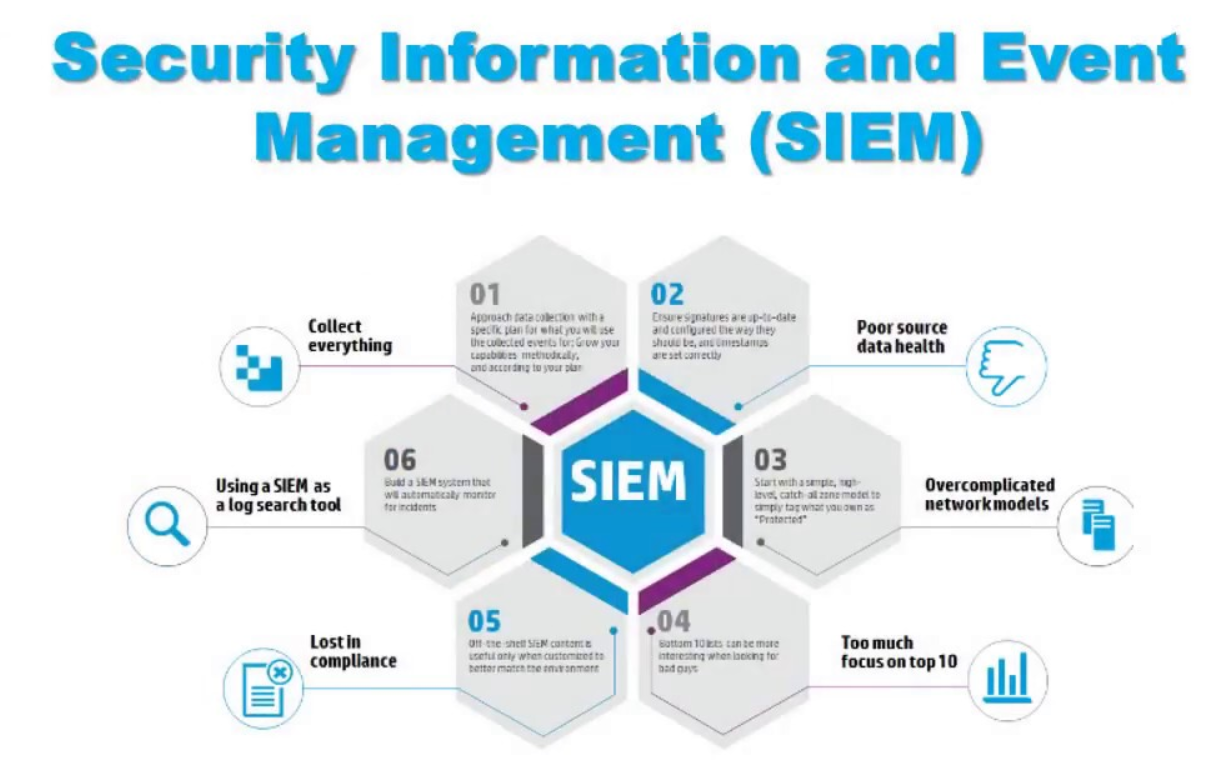
SIEM (Security Information and Event Management)
The more insight you have into your business operations, the safer you are. Security Information and Event Management Systems are crucial solutions for the digital world. They’re designed to tie your systems together and provide a more comprehensive view of IT security.
By 2021, the SIEM market will be worth $5.93 billion according to market analytics from Technavio. While every vendor has their own take on what SIEM services should include, there are some tools available that are more popular than others.
Here, we’ll look through some of the best SIEM tools that you can try in 2020.
10. RSA NetWitness
A complete network analytics solution, brimming with features to simplify your security strategy, RSA NetWitness is ideal for larger companies. Inside the software, you’ll find information about your business collected from various capture points, threat intelligence solutions, and computing platforms. There’s also an advanced threat detection feature which combines data science techniques with behavioral analysis.
The advanced response system offered by RSA serves to eliminate threats before they have a chance to disrupt your business. However, many users agree that there’s a steep learning curve. If you’re looking for something simple, this may not be it.
9. AlienVault USM
Intended for small to mid-sized companies in need of better security, AlienVault USM delivers state-of-the-art threat intelligence. Recently, AlienVault joined forces with AT&T to upgrade their cybersecurity portfolio. Your AlienVault SIEM system will be available either as a hardware or virtual appliance, depending on your needs. There’s also the option to access a cloud-based version of the product.
The USM offers intelligence information from a host of third-party vendors and services. There are also 150 built-in customizable reports available which adhere to standards like SOX and HIPAA. Based on open architecture, USM offers a highly flexible solution that can adapt to suit your needs over time.
8. ELK
Easily one of the most popular SIEM solutions on the market, ELK is otherwise known as the “Elastic Stack”, a selection of products combined from 3 vendors to provide a full SIEM solution. The ELK technology comes to you from Logstash, Elasticsearch, and Kibana. All 3 tools play a different part in your analytics strategy.
The ElasticSearch implementation provides the engine you need for easily storing data, while LogStash collects your information wherever it might be. Last, but not least, Kibana delivers the visuals that you need, bringing together one of the top analytics systems on the market.
7. IBM Security QRadar
IBM is a well-established name in the security and technology worlds. Their QRadar SIEM solution is available to deploy as a virtual appliance, software, or hardware. Additionally, QRadar threat intelligence offers both access to open feed intelligence, and Security X-Force via a paid subscription. The main thing that makes QRadar so appealing is its extensibility. There are plenty of additional modules you can build into your experience for data ingestion, vulnerability management, and risk control.
Designed to be both robust and flexible, QRadar is an excellent solution for monitoring the velocity and volume of data in an enterprise system. QRadar also has particularly powerful search functionality, though you may need to know a little about SIEM to take advantage of them.
6. MicroFocus ArcSight ESM
MicroFocus is a “ESM” product but often sold as a SIEM strategy. A mature system for larger enterprises, the ArcSight ESM is particularly well-suited to larger companies in the regulated and commercial environments. The technology supports a plan for server-based deployment that many organizations feel comfortable with. The basic SIEM features from MicroFocus ensure that you can monitor and handle a wide range of data sources in real time.
ArcSight ESM also offers intelligence from a multitude of third-party data sources. For larger organizations, it’s an excellent product if you have a large national or even global infrastructure. ArcSight not only identifies potential threats in your system, but it also gives you the tools you need to fix those issues.
5. LogRhythm
LogRhythm is a small but reliable player in the SIEM market, capable of offering exceptional services to mid-to-large enterprises. The solution comes with various deployment options, including distributed and bundled components, and virtual appliances. LogRhythm benefits from a host of features that competitors lack, including threat detection based on geolocation. There’s also built-in network forensics available, and 800 reporting formats.
Alongside a flexible and decentralized architecture, LogRhythm also provides one of the most powerful and diverse portfolios of security features on the market. However, it does require extensive networking and application configuration.
4. McAfee Enterprise Security Manager
When it comes to excellent analytics, McAfee offers some of the best tools on the market. The McAfee SIEM service allows companies to collect a wide range of logs across multiple devices with ease. What’s more, the McAfee correlation engine compiles various data sources effectively and efficiently into in-depth reports.
With the full McAfee package, you also get access to Business Technical Support and Enterprise Tech Support. McAfee will even send a support account manager to your company twice a year for routine check-ups. McAfee is also one of the leaders in the 2018 Gartner Magic Quadrant report for Security Information and Event Management.
3. Splunk
One of the best-known tools in the log file management world, Splunk is a SIEM system available via three service levels. The lowest-price level of Splunk doesn’t show live alerts but can deal with data in your log files. However, you can easily upgrade the level of insight that’s available by accessing a higher service tier.
Easy to use and understand, Splunk is a fantastic addition to any security and analytics strategy. All versions of the software come with a data analyzer built-in, which means that companies can efficiently sort through and filter records read from files. There’s also an Asset Investigator module to show you alerts from an in-depth device perspective.
2. SolarWinds Log and Event Manager
SolarWinds is a SIEM product from a company that delivers an extensive range of fantastic network management tools. The professional log management tool is one of the best in the world, and the Log & Event manager builds on that. The solution ensures that you can keep tabs on your log files with ease and receive instant alerts if anything suspicious happens. This will prevent intruders from covering their tracks and deleting log file records.
Another security feature of SolarWinds is that it can also manage your memory stick storage. The reporting tool built in with SolarWinds comes with pre-written formats compliant with numerous data integrity standards. Whether you’re worried about PCI DSS, HIPAA, ISO, or anything else, you should be covered.
1. Securonix
A next-generation SIEM platform that combines log management solutions with open data tracking, Securonix gives you everything you need for analytics. From unlimited scalability so that you can adapt your system to grow with your business, to behavioural analytics and machine learning built-in, you’ll have full peace of mind for your organization. There’s also the option to have your SIEM delivered as a “Cloud as a service” solution.
Securonix has also made a name for themselves as an official market leader in next-generation SIEM solutions. They were a Market Leader for the Gartner 2018 Security Information and Event Management Magic Quadrant.
For more details for SIEM requirement please contact us on
 Firewall Security Company India Complete Firewall Security Solutions Provider Company in India
Firewall Security Company India Complete Firewall Security Solutions Provider Company in India












