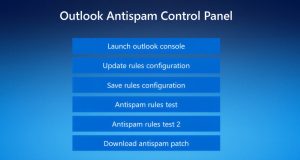
Fake Tech Support Spam Deploys Customized Havoc C2 Across Organizations https://firewalls.firm.in/wp-content/uploads/2026/03/outlook.jpg Threat hunters have called attention to a new campaign as part of which bad actors masqueraded as fake IT support to deliver the Havoc command-and-control (C2) framework as a precursor to data exfiltration or ransomware attack. The intrusions, identified by Huntress last month across five partner organizations, involved the ...
Read More »Vulnerabilities & Exploits
Building a High-Impact Tier 1: The 3 Steps CISOs Must Follow
Building a High-Impact Tier 1: The 3 Steps CISOs Must Follow https://firewalls.firm.in/wp-content/uploads/2026/03/tier1.jpg Every CISO knows the uncomfortable truth about their Security Operations Center: the people most responsible for catching threats in real time are the people with the least experience. Tier 1 analysts sit at the front line of detection, and yet they are also the most vulnerable to the ...
Read More »Microsoft Warns OAuth Redirect Abuse Delivers Malware to Government Targets
Microsoft Warns OAuth Redirect Abuse Delivers Malware to Government Targets https://firewalls.firm.in/wp-content/uploads/2026/03/ms-login.jpg Ravie LakshmananMar 03, 2026Phishing / Malware Microsoft on Monday warned of phishing campaigns that employ phishing emails and OAuth URL redirection mechanisms to bypass conventional phishing defenses implemented in email and browsers. The activity, the company said, targets government and public-sector organizations with the end goal of redirecting victims ...
Read More »⚡ Weekly Recap: SD-WAN 0-Day, Critical CVEs, Telegram Probe, Smart TV Proxy SDK and More
⚡ Weekly Recap: SD-WAN 0-Day, Critical CVEs, Telegram Probe, Smart TV Proxy SDK and More https://firewalls.firm.in/wp-content/uploads/2026/03/recap-main.jpg Ravie LakshmananMar 02, 2026Cybersecurity / Hacking This week is not about one big event. It shows where things are moving. Network systems, cloud setups, AI tools, and common apps are all being pushed in different ways. Small gaps in access control, exposed keys, and ...
Read More »How to Protect Your SaaS from Bot Attacks with SafeLine WAF
How to Protect Your SaaS from Bot Attacks with SafeLine WAF https://firewalls.firm.in/wp-content/uploads/2026/03/safeline.jpg Most SaaS teams remember the day their user traffic started growing fast. Few notice the day bots started targeting them. On paper, everything looks great: more sign-ups, more sessions, more API calls. But in reality, something feels off: Sign-ups increase, but users aren’t activating. Server costs rise faster ...
Read More »Thousands of Public Google Cloud API Keys Exposed with Gemini Access After API Enablement
Thousands of Public Google Cloud API Keys Exposed with Gemini Access After API Enablement https://firewalls.firm.in/wp-content/uploads/2026/03/gemini.jpg New research has found that Google Cloud API keys, typically designated as project identifiers for billing purposes, could be abused to authenticate to sensitive Gemini endpoints and access private data. The findings come from Truffle Security, which discovered nearly 3,000 Google API keys (identified by ...
Read More »ClawJacked Flaw Lets Malicious Sites Hijack Local OpenClaw AI Agents via WebSocket
ClawJacked Flaw Lets Malicious Sites Hijack Local OpenClaw AI Agents via WebSocket https://firewalls.firm.in/wp-content/uploads/2026/03/opem.jpg OpenClaw has fixed a high-severity security issue that, if successfully exploited, could have allowed a malicious website to connect to a locally running artificial intelligence (AI) agent and take over control. “Our vulnerability lives in the core system itself – no plugins, no marketplace, no user-installed extensions ...
Read More »RBI summons executives over forex card breach
RBI summons executives over forex card breach https://etimg.etb2bimg.com/thumb/msid-128873075,imgsize-98498,width-1200,height=627,overlay-etciso,resizemode-75/data-breaches/rbi-summons-executives-over-forex-card-breach.jpg The Reserve Bank of India (RBI) has summoned senior officials of Yes Bank following a significant data breach involving the Yes Bank-BookMyForex multi-currency forex card, two people aware of the development told ET. Card details and CVV numbers of several users were allegedly compromised. The central bank has sought a detailed explanation ...
Read More »ScarCruft Uses Zoho WorkDrive and USB Malware to Breach Air-Gapped Networks
ScarCruft Uses Zoho WorkDrive and USB Malware to Breach Air-Gapped Networks https://firewalls.firm.in/wp-content/uploads/2026/02/keys.jpg Ravie LakshmananFeb 27, 2026Malware / Surveillance The North Korean threat actor known as ScarCruft has been attributed to a fresh set of tools, including a backdoor that uses Zoho WorkDrive for command-and-control (C2) communications to fetch more payloads and an implant that uses removable media to relay commands ...
Read More »Identity Prioritization isn’t a Backlog Problem – It’s a Risk Math Problem
Identity Prioritization isn’t a Backlog Problem – It’s a Risk Math Problem https://firewalls.firm.in/wp-content/uploads/2026/02/main.gif Most identity programs still prioritize work the way they prioritize IT tickets: by volume, loudness, or “what failed a control check.” That approach breaks the moment your environment stops being mostly-human and mostly-onboarded. In modern enterprises, identity risk is created by a compound of factors: control posture, ...
Read More » Firewall Security Company India Complete Firewall Security Solutions Provider Company in India
Firewall Security Company India Complete Firewall Security Solutions Provider Company in India